Bits, Banks and Burglars
Most stolen digital data has really just been copied. A typical digital theft is the stolen emails of the Democratic National Committee (DNC). These emails were considered private when written, but were later accessed by hackers and then released to the public. This sort of viewing of private data is often referred to as data theft, but at the time it was stolen, nothing went missing from the DNC and no one knew cyber burglars had taken their emails.
Traditional thefts, where someone gains something and someone else loses something, do happen online and primarily with digital currencies like bitcoin. Digital currencies are built on technology that allows data to be possessed by only one person at a time, and that is significant. But the digital implementation is very different from the real world and those differences make it much harder to reclaim stolen digital currency.
Quick Primer on Digital Currency
Here are the five key things you need to know about digital currency in order to understand how it gets transferred and why it’s hard to get it back:
- Many currencies: There are at least 21 active digital currencies, according to Wikipedia. The two most popular are Bitcoin and Ethereum, but the list goes on.
- The blockchain: These currencies work on top of a technology called the blockchain. Think of every bitcoin as having a serial number, much like physical currency has serial numbers, but every one of these is tracked so that only one person can possess it at a time. The blockchain is the distributed ledger that tracks every transfer and where each serial number currently resides. Everyone can view this ledger, but no one owns or controls it. New transactions can only be added to the end.
- Pseudonymous: Anyone can create a wallet (or multiple wallets). A wallet is like a bank account for digital currency and it has an account number. Rather than hand out this account number, wallet holders can generate addresses, to be used in transactions once or many times, which are like account number aliases. These help protect privacy. A wallet is not tied to a person’s real identity, but in the process of buying something or converting real currency, the owner may have to disclose her name and address. The person on the other end of the transaction can then tie the address to a person. Also, since all transactions are public, determined investigators can follow money flows and tie addresses together and discover who is behind them.
- Secret-based security: You can give out instructions for others to send currency to one of your wallet’s addresses, but to take money out of the wallet, you have to possess the secret information, the private key, associated with it. Anyone who can access this secret information, which could include malware or hackers on your computer, can send money elsewhere. If you trust your digital money to one of the many eWallet companies or to currency brokerages, it becomes easier to use and to exchange. This can come with features that bring extra privacy and convenience, but you must trust the company to keep your wallet safe. If your broker gets hacked, attackers may potentially get full access to your accounts. And unlike with stolen credit card numbers, the liability is all yours.
- Irreversible transactions: There is no way to void or otherwise undo a transaction. Once currency has been transferred to another party, the original party cannot get it back. Police cannot seize it unless they can identify the thief and get access to their wallet by getting access to their secret. In short, there’s no undo and no facility for recovering stolen money.*
* See “The DAO” section below for the exception to this statement.
Notable Digital Currency Thefts
In recent times, we’ve seen a number of massive digital currency thefts with some pretty fascinating back stories and lessons. Here’s a summary of the most interesting thefts:
- Bitfinex: The Bitfinex exchange has temporarily shut itself down while it investigates the theft of some US$77m worth of bitcoin from its users’ wallets. Note: the US dollar amount cited varies based on when the conversion is done. Only bitcoin was affected so users storing other crypto currencies on Bitfinex should be able to withdraw their money when the exchange reopens. There’s no evidence of what happened, but rumors are swirling online that requirements from regulators lead to lowered security. Quartz has a great writeup on what’s known so far along with this handy chart of the top bitcoin thefts from bitcoin exchanges:
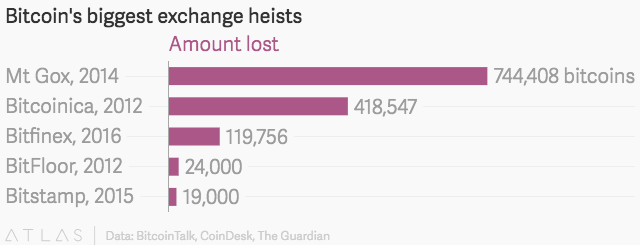 Credit: Quartz
Credit: Quartz
- The DAO: The Decentralised Autonomous Organization (The DAO) was something akin to a democratic venture capital fund where anyone could be a member by buying in with the digital currency Ethereum and then voting on how to use the joint money to fund projects and startups. The DAO sparked interest after it raised US$150m from 11,000 people in a short time. However, shortly thereafter, US$53m of that money was stolen via a bug in the software that autonomously runs the organization. The underlying currency, Ethereum, attempted something no other digital currency has done before; it was “forked”, creating a new one in its place and leaving the old one behind. They recreated the ledger of all transactions conducted in the original currency, but excluded the transactions associated with the theft. This rewriting of history (well, copy-and-modify of history) essentially defeated one of the core tenets of digital currency: that transactions can’t be undone. Accomplishing this required creating two divergent copies of the global blockchain ledger for the currency, effectively creating two currencies. This has incited a small rebellion that continues to create problems.
- Mt. Gox: One of the early exchanges that held onto digital wallets on behalf of its users was a Japanese company called Mt. Gox. In 2014, Mt. Gox suddenly declared bankruptcy. Some $450 million U.S. Dollars worth of BitCoin (at the exchange rate at the time) had vanished. Apparently the money had been siphoned off for years without anyone noticing. To this day no one knows what happened to the money. A lengthy process was initiated to return a portion of the remaining $US90m to customers, but after an expenditure of US$55m for legal fees, no one has yet seen a dime.
- ShapeShift: At just US$230k in losses, this story is less decorated with zeros than some of the others, but is a fascinating look at trust models and money, particularly in a world where transactions cannot be reversed. A disgruntled insider sold information to hackers that gave them the keys needed to compromise ShapeShift’s systems and steal their digital currency reserves. In security risk analysis, every link in the chain of access needs to be examined, from the code and the servers to the people whose jobs it is to secure those assets.
Summary
Before digital currencies, financial institutions that fell prey to a malicious insider or exploited software bug would result in the copying (theft) of customers’ personal data, financial records and possibly even transfers out of their accounts. In many cases, when money is stolen, it can later be reclaimed by law enforcement and agreements between banks. With digital currencies, a malicious insider or software bug can transfer money that cannot be recovered unless authorities are able to find the perpetrator and get full access to their secret keys.
That said, in many ways digital currencies are more secure and more trustworthy. If you can protect your wallet’s secret key, no one can seize or steal your money.
These lessons are important because traditional banks are embracing the technology underlying these digital currencies to build stock exchanges and marketplaces of the future. The technology has a lot of promise, but there’s much still to learn and improve. Without a doubt, we’ll continue to see high profile, large sum thefts of digital currency.