Data Control Platform
Developer tools to control access to your data with encryption to build minimal trust, zero-trust, and end-to-end encrypted applications.
Comparing IronCore products? See our developer documentation for a comparison table, decision tree, and use-case examples.
Benefits of data control
- Provable Access: It’s the difference between “I think” my data is safe and “I know” who has access to my data. When data is controlled, there’s no doubt about who can see the data. The proof is in the math.
- Monitored Use: Knowing who can see the data is not enough. It’s important to know who is actually looking at data, when, and from where so you can monitor forqunset unusual activity and detect abuse.
- Revocation: Granting access should not be a one-way street. What is granted should be revokable for any reason. Without revocation, you are left asking someone nicely to please delete your data. Good luck with that.
- Everywhere: Having control of your data means controlling all copies of it – whether shared with third parties, stored on cloud servers, residing in a database, shared file storage, or on client devices. IronCore’s data controls work everywhere and travel with the data.

Key use cases
Zero-trust data systems
Go beyond zero-trust networks and take your security to what you're protecting: the data. Zero-trust data allows companies to survive network breaches without customer impact or disclosure through the use of cryptographic access controls and end-to-end encryption.
Secure sharing in the cloud
Sometimes even sensitive data must be shared with partners, auditors, and data consortiums. With IronCore’s Data Control Platform, data can be shared but still monitored and effectively pulled back if necessary. No more asking nicely and hoping.
Right to be forgotten
Deleting users is harder than it seems. What about backups and copies across services? What if you still need the history so stats don't change? IronCore crypto-shredding solves these issues with a simple "revoke."
Data residency
Stop spinning up data-centers to meet residency requirements. Use cryptography that can keep keys in-country while letting encrypted data replicate globally. The data can only be decrypted in-country.
End-to-end encrypted video conferencing
Most cryptography is good at one-to-one or one-to-small-static-group scenarios. IronCore fixes this with strong end-to-end encryption suitable for video conferencing with large dynamic groups. There is no upper bound on conference size. All of the hard stuff is handled for you. Read the white paper.
End-to-end encrypted group chat
Group chats in applications like Slack are difficult to encrypt and scale without losing functionality. But with IronCore's group encryption, device-level key management, and extra features like text search, you can have your company chat and secure it, too.
Internet of Things (IoT)
The IoT space is a case study in poor security. Many connected devices don't even bother with the basics. But for devices that collect sensitive data, as with healthcare or military applications, the data should be encrypted before it ever leaves the device. We can help.
Blockchain
Whatever you may have heard, blockchains are not private. Data on a blockchain stays there forever. But what if you could change who could access that data even though the data itself is immutable? This is the power of data control in a blockchain world. The owner determines access and can change it. And this goes double for shared wallets used by organizations.
How the Data Control Platform works
Core features
Automatic key management
Encrypting data is easy. But then what do you do with the key? IronCore handles all of the hard parts around managing keys, linking to identities, generating new keys, rotating, lifecycle management, and more.
Device management
Every client (app + device) that needs to interact with controlled data has its own key. A user controls a collection of their devices. Adding new devices and revoking lost, stolen, or temporary devices (like web browsers) is trivial.
Ease-of-use
IronCore provides powerful cryptography for non-cryptographers. We remove as many decisions as possible so developers need only determine what to encrypt and where the encrypt/decrypt operations need to take place.
Audit trails
IronCore uses a multi-party computation that requires a call to a zero-trust server before any data can be decrypted. The generated audit logs can’t be bypassed, and each request is cryptographically signed by the user for tamper-evidence.
Encrypted search
IronCore supports encrypted search of substrings where the client sends an encrypted query and the server returns encrypted results without learning about the search or the results.
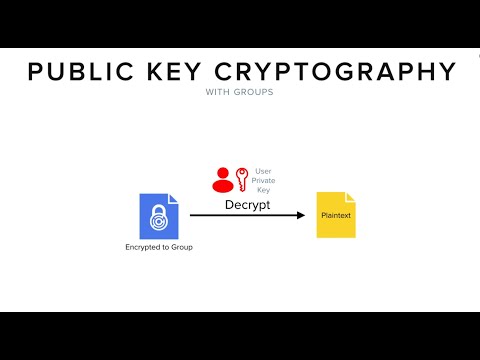
Scalable groups
IronCore uses public-key cryptography based on elliptic curves. Traditionally this only works well for point-to-point encryption schemes, but with IronCore, you can encrypt to groups and dynamically change the group membership. Groups can be any size and encrypt operations are constant time operations.
Policy-driven encryption
IronCore offers a policy feature that allows the determination for who (which users or groups) to encrypt to to be determined based on the type of data being encrypted. This is the developer-proof mode that puts the security team in charge.
Multi-tenant native
With projects and segments, IronCore easily supports different identity realms and applications so you don’t have to work hard to integrate our products into a multi-tenant SaaS application.
Revocation
When data is shared with a group, it’s trivial to remove a member and thereby revoke access for that user. Doing this does not require touching files that were encrypted to the group, which makes it a nearly instantaneous change.
Broad platform and language support
End-to-end encryption isn’t too useful when one of the ends can’t encrypt or decrypt the data. With IronCore, data can be processed on all major cloud platforms, desktop operating systems, mobile devices, and browsers. In addition, a variety of programming languages are fully supported and others can be upon request.
| Cloud Platforms | Google Compute Platform, Amazon Web Services, Microsoft Azure, Thales |
|---|---|
| Browsers | Chrome, Safari, Firefox, Edge, WebAssembly |
| OSes | Android, iOS |
| Desktop OSes | Linux (with libstd or musl), Mac, Windows |
| Chips | ARM32, ARM64, x86, x86-64 |
| Languages | Java, Scala, Rust, NodeJS, JavaScript, TypeScript, C, C++ |
Broad data support from files to fields
The Data Control Platform can be used to control data on a per-row, per-column, per-field, per-object, per-file, or per-big-data-partition basis depending on your needs. We can encrypt large files or small data fields in SQL databases. Below is a partial list of the supported backend data storage systems that we support.
| File Storage | AWS S3, GCP FileStore, Azure Blob Storage, Linux FileSystem, NFS, NetApp |
|---|---|
| SQL Databases | MySQL, Oracle, SQL Server, Postgres, AWS RDS, Google Cloud SQL, Azure SQL |
| Big Data | Hadoop, Apache Spark, Snowflake, Cassandra |
| NoSQL Databases | MongoDB, CouchDB, Neo4j, BigTable, Firebase, Supabase |
Privacy guarantee
Completely blind services
IronCore never sees your data. All data encryption and decryption is done inside your app and you store the encrypted data.
Some products operate entirely offline while others use our cloud services. In either case, IronCore is never in a position to see unencrypted data, to decrypt encrypted data we hold, or to see your keys.
Be compliant
Most regulatory and contractual mandates require strong data protection measures including encryption, access monitoring, and tight control of permissions. The Data Control Platform brings all of this to your most regulated and sensitive data.
GLBA and SOX
Being a public company means being very private with strategic plans, unreleased financial data, unannounced acquisitions, and more. Control your data and you control your liability.
HIPAA and HITECH
Personal health data is some of the most protected data worldwide and in the US, penalties for failing to protect this data are steep. Stop unauthorized access by your biggest threat: curious insiders.
CJIS
Criminal justice data must be stored securely and with tight access control mechanisms. Unfortunately, this data gets emailed around and shared in ways that cause all control to be lost. We can help with this.
GDPR and CCPA
GDPR and CCPA require careful handling of data and have steep penalties if consumers' private information is leaked. GDPR goes even farther by requiring “data protection by design and by default” (article 25). We can help with all of the data protection, access control, and audit trail requirements.
PCI-DSS
PCI requires that all payment data be encrypted and that payment providers “develop and maintain secure systems and applications.” We help providers by not just handling the data they hold internally, but controlling who can access data as it flows between parties.
ITAR and EAR
ITAR and EAR protect sensitive Government and Military information, but both now allow some data to be stored in the cloud and even outside the country if the data is end-to-end encrypted. We make ITAR and EAR-compliant functionality easy to build into applications.
FERPA
Data relating to minors is protected by FERPA and by a patchwork of strict state privacy laws in the U.S. Many countries go even farther. Claiming to be FERPA-compliant without data control is like claiming to be a superhero when you have no powers. You just hope the villains are weaker than you are.
Learn more
Whether it’s your sensitive intellectual property, financial information, healthcare information, consumer personal information, or just non-public information at a public company, you need to protect data that can be abused.
Protect your data with non-transparent, application-layer encryption that provides the security and privacy for the data you hold, regardless of where that data lives.