Baby Steps with NY's New Financial Cybersecurity Regs
Banks, insurance companies and other financial services companies in New York will soon be subject to new, stronger regulations around cybersecurity. The latest draft has to undergo another 30 day feedback period before it can go into effect.
The current draft waters down some of the provisions in the previous draft after criticism that they were too burdensome for smaller companies.
The meat of the regulation requires companies to design and implement a cybersecurity program and related policies, and mandates a CISO to oversee them.
Beyond the big points, two smaller provisions caught our eye.
Application Security Requirements
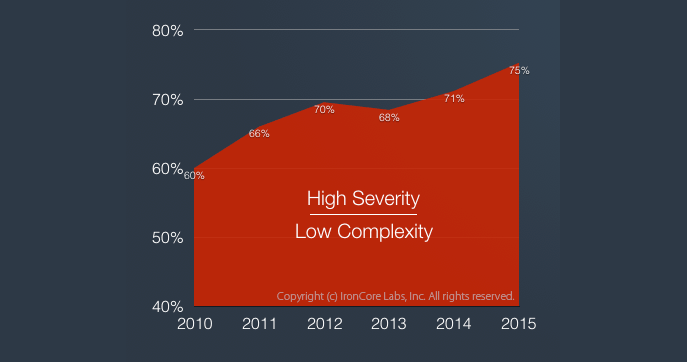
Organizations must take steps to add security to their in-house applications. They also must assess the security of all applications and services that they purchase:
Each Covered Entity’s cybersecurity program shall include written procedures, guidelines and standards designed to ensure the use of secure development practices for in-house developed applications utilized by the Covered Entity, and procedures for evaluating, assessing or testing the security of externally developed applications utilized by the Covered Entity within the context of the Covered Entity’s technology environment.
Companies who sell software to financial services companies in New York will now see a new patchwork of requirements from those companies around security. Because that framework is left to each company, vendors will have unique hoops to jump through for each sale.
Encryption Requirements (and Exceptions)
The regulation also requires encryption of “Nonpublic Information,” which is defined as basically any personally identifiable information, health information, and any sensitive information whose theft could be damaging to the business:
… each Covered Entity shall implement controls, including encryption, to protect Nonpublic Information held or transmitted by the Covered Entity both in transit over external networks and at rest.
Unfortunately, the three following clauses water down that requirement by allowing exceptions at the discretion of the CISO provided those exceptions are re-evaluated annually. For example:
To the extent a Covered Entity determines that encryption of Nonpublic Information in transit over external networks is infeasible, the Covered Entity may instead secure such Nonpublic Information using effective alternative compensating controls reviewed and approved by the Covered Entity’s CISO.
These exceptions are likely a nod to existing legacy applications that don’t use encryption. Unfortunately, by giving companies a pass, those legacy applications will remain a major security problem without a strong incentive to fix the issue.